SSH Config
This is part of the mini-series OpenSSH for Devs.
An SSH config let’s you set options you use often (e.g., the user to login as or the port to connect to) globally or per-host. It can save a lot of typing and helps make SSH Just Work.
Example
Instead of typing:
ssh -p734 teamaster@sencha.example.com
You can type:
ssh sencha
By having this in your ~/.ssh/config:
Host sencha
HostName sencha.example.com
Port 734
User teamaster
What’s a per-user SSH config?
In your home is a .ssh directory. This is where your SSH keypair and known_hosts1 files are. This directory is not made of unicorns. Create a file named config and your SSH tools2 will use it’s settings.
If your laptop username is different than the one on your remote hosts, create it with:
User jon.postel
If you use a non-standard SSH port to avoid the bots, create it with:
Port 22022
Have different settings for different hosts? No problem. Just keep in mind the first match wins and put specific settings before generic ones:
# ancient box we never upgraded
Host host1.example.com
User oldusername
# still on port 22
Host *.example.com
Port 22022
ForwardAgent yes
# defaults for all hosts
Host *
User bofh
It gets better
You’re probably familiar with the dance you do when connecting to a host for the first time:
$ ssh host1.example.com
The authenticity of host 'host1.example.com (192.0.2.101)' can't be established.
RSA key fingerprint is 39:9b:de:ad:9e:be:ef:95:ca:fe:1b:53:b0:00:00:b5.
Are you sure you want to continue connecting (yes/no)?
It looks impressive, but it’s worthless. If you’re worried about man-in-the-middle attacks, there are much better things to do. Start by disabling password authentication3 and require people to have an SSH key on the server. Expecting people to check these hashes means you’ve already failed.
To get rid of the dance add something like:
Host *.compute-1.amazonaws.com
StrictHostKeyChecking no
First time connections will give you a warning, but you’ll make it in.
Aliases
You can create aliases4 by using Host to match a name and HostName to say where to connect.
Host web1
HostName ec2-192-0-2-42.compute-1.amazonaws.com
The advantages over modifying /etc/hosts are you don’t need to be root and SSH will use the same host key for web1 and ec2-192-0-2-42.compute-1.amazonaws.com. The disadvantage is that only SSH tools see this. For example, your browser has no idea web1 is an alias for that EC2 host. Because of this, I sometimes create both the SSH alias and hosts entry for the best of both worlds.
Options
There are a lot of options, but these are the ones I’ve seen used most:
- Host — Matches the hostname argument. Accepts patterns and causes options following it to apply only to hosts matching the pattern.
- User — Username to connect with.
- Port — Port to connect to.
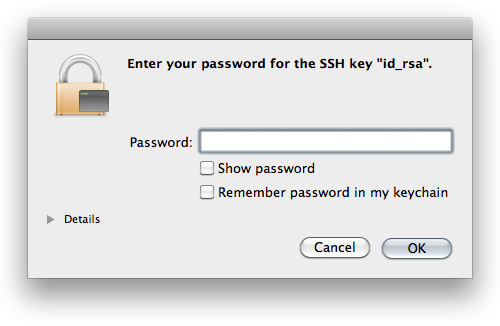
- ForwardAgent — Set to
yes to turn on SSH agent forwarding.
- StrictHostKeyChecking — Set to
no to skip the “authenticity of host” dance.
- HostName — Server to connect to. Used to create an alias from Host to another remote server.
Do you have a favorite option not mentioned here? You should post a comment or send me a message.
-
The known_hosts file contains the keys for all the remote hosts you’ve connected to. The stored key is compared to the remote key when you connect to warn of a man-in-the-middle attack. ↩
-
ssh, scp, sftp, sshfs, well-written paramiko based Python tools, and probably more. ↩
-
In the server’s sshd_config set PasswordAuthentication no. Contact me if you are interested in a post on securing the SSH server. ↩
-
I made this term up. There may be a better one. ↩